In the world of cryptocurrency, security is paramount. With the rise of digital currencies, it is crucial to find a reliable and secure wallet to store your valuable assets. One such wallet that has gained popularity is Exodus Wallet. Exodus Wallet is a user-friendly software wallet that allows users to securely store, manage, and trade various cryptocurrencies. It offers a sleek and intuitive interface, making it an attractive choice for both beginners and experienced traders.
Understanding the Security of Exodus Wallet
The security of a cryptocurrency wallet is of utmost importance. Exodus Wallet understands this and has implemented several measures to ensure the safety of your digital assets. One such measure is the use of strong encryption to protect your private keys. These private keys are stored locally on your device and are never sent to Exodus servers, minimizing the risk of them being compromised.
Additionally, Exodus Wallet allows you to set up a 12-word recovery phrase during the initial setup process. This recovery phrase acts as a backup for your wallet and can be used to restore your funds in case your device is lost or damaged. It is crucial to keep this recovery phrase safe and secure, as anyone with access to it can potentially gain control over your wallet.
Furthermore, Exodus Wallet regularly updates its software to fix any security vulnerabilities that may arise. These updates are crucial in ensuring that your wallet remains secure and protected against any potential threats.
The Hack Incident and Its Impact
Unfortunately, even with robust security measures in place, no system is completely immune to hacking attempts. In 2020, Exodus Wallet fell victim to a hack that resulted in the loss of funds for some of its users. The hack was a result of a targeted attack on the infrastructure that Exodus Wallet relies on.
The impact of the hack was significant, with many users losing their hard-earned cryptocurrencies. The incident not only led to financial losses but also shattered the trust that users had in Exodus Wallet’s security measures. This incident served as a wake-up call for both Exodus Wallet and its users, highlighting the importance of constant vigilance in the world of cryptocurrency.
Steps Taken by Exodus Wallet To Address the Hack
In the aftermath of the hack, Exodus Wallet took immediate action to address the issue and mitigate any further damage. The team at Exodus Wallet worked tirelessly to identify the vulnerability that was exploited and implemented measures to patch it. They also conducted a thorough investigation to understand the extent of the hack and identify the affected users.
Exodus Wallet took responsibility for the incident and promptly communicated with its users, providing updates on the progress of the investigation and steps taken to address the hack. They also offered support and guidance to affected users, ensuring that they had the necessary resources to recover from the incident.
Lessons Learned From the Exodus Wallet Hack
The Exodus Wallet hack serves as a valuable lesson for both wallet providers and cryptocurrency users. It highlights the need for constant vigilance and the importance of staying informed about the latest security practices. Here are some key lessons that can be learned from this incident:
- Regularly update your wallet software: Keeping your wallet software up to date is crucial in protecting your digital assets. Software updates often include security patches that address vulnerabilities and protect against potential threats.
- Secure your recovery phrase: Your recovery phrase is the key to restoring your wallet in case of loss or damage. It is essential to keep it safe and secure, preferably in offline storage.
- Be wary of phishing attempts: Hackers often use phishing techniques to trick users into revealing their private keys or recovery phrases. Always double-check the authenticity of any communication or website before entering sensitive information.
- Diversify your storage: Consider diversifying your cryptocurrency storage by using multiple wallets or cold storage solutions. This reduces the risk of losing all your funds in case of a hack or technical failure.
Tips to protect your cryptocurrency wallet from hackers
While no system can guarantee complete protection against hackers, there are several steps you can take to enhance the security of your cryptocurrency wallet. Here are some tips to help protect your digital assets:
- Choose a reputable wallet: Research and choose a wallet from reputable providers, known for their strong security measures and positive user reviews.
- Enable two-factor authentication (2FA): Two-factor authentication adds an extra layer of security to your wallet by requiring a second form of verification, such as a code sent to your mobile device, in addition to your password.
- Use a hardware wallet: Consider using a hardware wallet, which is a physical device designed specifically for storing cryptocurrencies. Hardware wallets offer enhanced security by keeping your private keys offline and away from potential online threats.
- Keep your software up to date: Regularly update your wallet software and operating system to ensure you have the latest security patches.
Alternatives to Exodus Wallet for Secure Cryptocurrency Storage
If you have been deterred by the Exodus Wallet hack and are looking for alternative options for secure cryptocurrency storage, there are several reputable wallets available in the market. Some popular alternatives include:
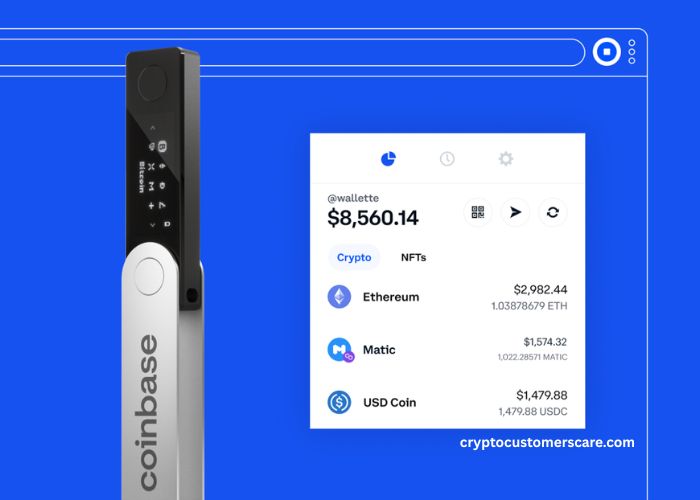
- Ledger Wallet: Ledger Wallet is a well-known hardware wallet that offers robust security features and supports a wide range of cryptocurrencies.
- Trezor Wallet: Trezor Wallet is another popular hardware wallet known for its excellent security measures and user-friendly interface.
- MetaMask: MetaMask is a software wallet that provides a secure and convenient way to manage your Ethereum-based cryptocurrencies. It offers browser extension and mobile app options for easy access.
Seeking Compensation for Losses Due to the Hack
If you were one of the unfortunate victims of the Exodus Wallet hack and suffered financial losses, you may wonder if you are eligible for compensation. The process of seeking compensation can vary depending on the circumstances and the policies of the wallet provider. It is essential to reach out to Exodus Wallet’s customer support for guidance and assistance in this matter.
How To Recover From a Cryptocurrency Wallet Hack
Recovering from a cryptocurrency wallet hack can be a daunting process, but it is not impossible. Here are some steps you can take to recover from a hack:
- Contact the wallet provider: Reach out to the wallet provider’s customer support to report the incident and seek guidance on the recovery process.
- Change your passwords and enable 2FA: Change your passwords for all relevant accounts and enable two-factor authentication to enhance the security of your accounts.
- Monitor your accounts: Keep a close eye on your accounts and transactions to identify any suspicious activity. Report any unauthorized transactions immediately to the wallet provider’s customer support.
- Consider legal action: In extreme cases where significant financial losses have occurred, you may want to consult with a legal professional to explore your options for seeking compensation or taking legal action against the hackers.
Conclusion
The Exodus Wallet hack serves as a stark reminder of the importance of security in the world of cryptocurrency. While no wallet or system is entirely immune to hacking attempts, taking proactive measures to protect your digital assets is crucial. By staying informed about the latest security practices, choosing reputable wallets, and implementing additional security measures such as two-factor authentication and hardware wallets, you can enhance the security of your cryptocurrency storage. Remember, the key to keeping your digital assets safe lies in constant vigilance and staying one step ahead of potential threats.